When deployed on Windows, the Pure1 PowerShell Module takes advantage of Windows-based certificates in the user (or specified) certificate store. On Linux or MacOS, it uses RSA private key pairs.
To relocate authentication on a Non-Windows machine to another non-Windows machine, you just copy the private key from wherever it is to the target. For Windows though you need to export the cert (which has a private key) from the certificate store, then you can copy the file to wherever.
In the latest release of the Pure1 PowerShell module (1.4.3.1) there is a new feature to do that for you–or at least simplify the process of exporting the cert with the right settings.
Let’s walk through exporting and then importing the cert. In a future post I will go into some of the other enhancements in this release in more detail.
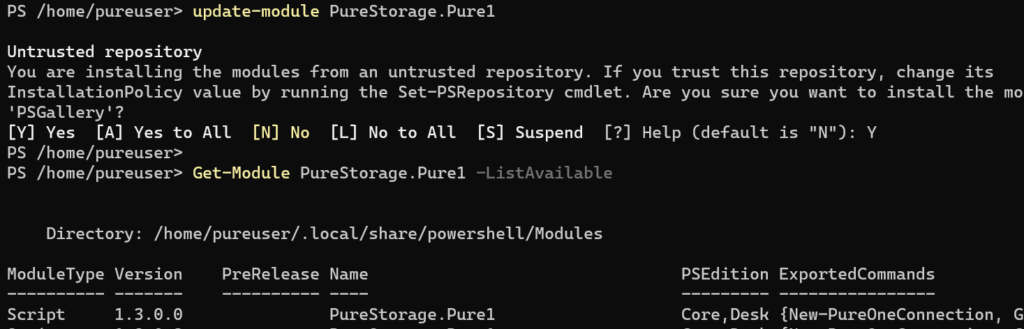
As always the repo is here (and release notes) and it is best installed/updated via the PowerShell Gallery:
install-module PureStorage.Pure1 or update-module PureStorage.Pure1
https://github.com/PureStorage-OpenConnect/PureStorage.Pure1
Continue reading “Exporting/Importing a Certificate with the Pure1 PowerShell Module”